What is an Operating System?
An operating system is a type ofsoftwarethat manages the hardware and software components of a computer system, all programmes, excluding firmware, require an operating system in order to function. Operating systems (OS) are found on any device that contains a computer, such as mobile phones, videogame consoles, web servers, and smart watches. The most popular desktop operating system today isMicrosoft Windows, with a total market share of 83.3%, followed by Apple’s macOS with 11.2%, and versions of Linux in third with 1.55%. In mobile devices, such as smartphones and tablets, Android by Google sits at 87.5% of worldwide market share, with Apple’s iOS at 12.1%.
Types of Operating System

Windows
Windows is the name given to the many versions of an operating system designed, developed, marketed and sold byMicrosoft. The first version of Windows was introduced in November 1985 as a graphical operating system shell in response to an increasing interest in graphical user interfaces.
As of 2016, Windows is still the most popular operating system on PC’s, but the exponential growth of Android smartphones has led to the sharp decline of Windows in mobile devices. In 2016, Microsoft released Windows 10 for PC’s, smartphones, and tablets, whilst a specialised version of Windows is used on Microsoft’s Xbox One games console.
Mac
The family of Macintosh operating systems is a graphical user interface designed by Apple Inc. for specific use on its series of Macintosh personal computers, and has been installed as standard on the devices since 2002. Apple’s first operating system debuted in 1984, and is now referred to as ‘classic’ Mac OS. Apple uses its current operating system, High Sierra, which has an entirely new architecture and annual updates on all of its device software including: iOS, watchOS, and tvOS.
Linux
Linux was originally created for personal computers in 1991 by Finnish-American software developer Linus Torvalds as an operating system modelled around the free and open-source development and distribution of software. Linux, although not as widely used on personal or handheld devices in the consumer market, is the leading operating system used on servers and mainframe computers, with a 99.6% market share of the Top500 supercomputers.
Android
Designed for use on touchscreen mobile devices such as smartphones and tablets, Android is a mobile operating system created entirely by Android Inc., which Google bought in 2005. The user-interface works on the principle of direct manipulation, and transforms touch gestures that correspond with real world actions, such as tapping, swiping, and pinching, to move on-screen objects.
iOS
Formerly known as iPhone OS, iOS is a mobile operating system created by Apple Inc. exclusively for its mobile and handheld devices such as iPhone, iPad, and iPodTouch. Boasting a total worldwide download of 130 billion, Apple’s App Store consists of more than 2.2 million iOS applications, and major versions of iOS software are released annually.
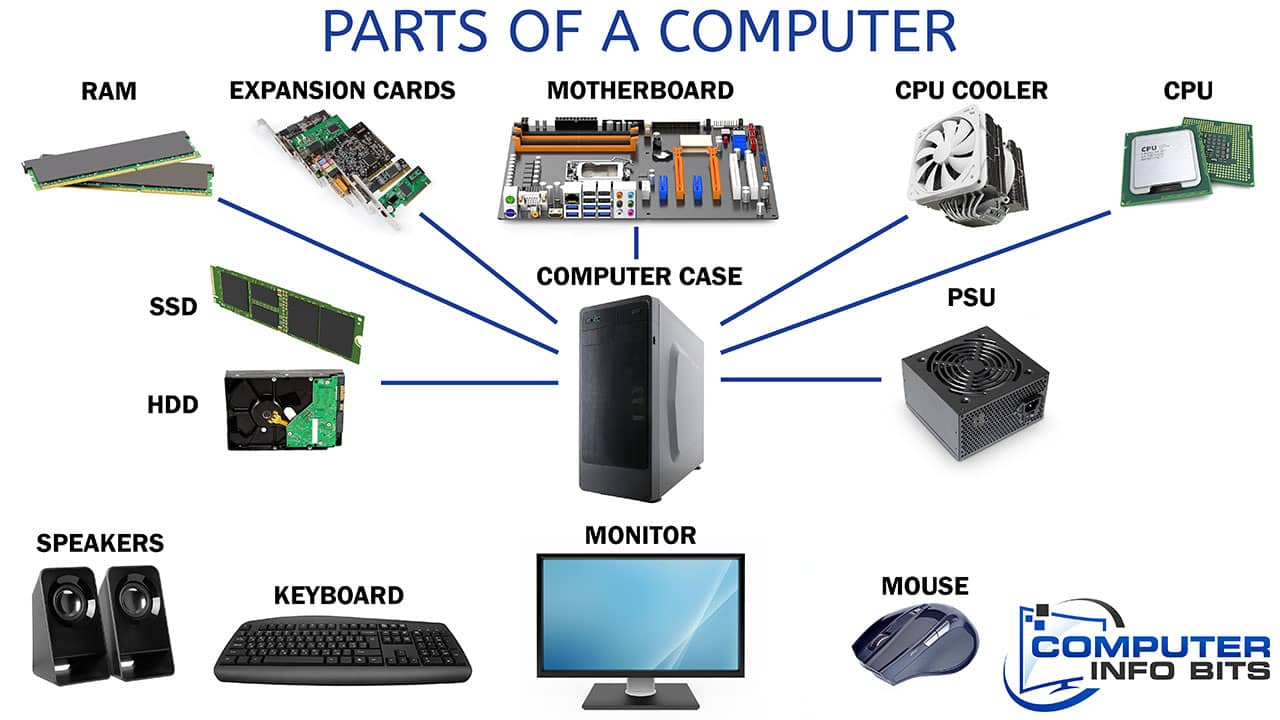
Types of Hardware
Desktops
A desktop computer is a personal computer designed to be used at a single location. They sit on, or near a desk or table due to their size and power requirements. The ‘computer’ is the tower that houses the power, motherboard and memory, which can be positioned horizontally or vertically, dependent on space available. Additional electronic components attach to the tower to allow the user to operate it, such as a key board, mouse, and crucially, the monitor.
There are also ‘all in one’ desktop computers that combine the tower and monitor into one unit. While desktops have long been the common configuration of computers, since the mid 2000s, laptop computers have taken higher prominence in the market, due to their portability.
Monitors
Also known as displays, a computer monitor is a visual display for computers that can be connected to a computer via VGA, HDMI, DisplayPort, Thunderbolt or DVI connections. Originally, computer monitors were used for data processing, while television receivers were used for entertainment. From the 1980s onwards, both televisions and computer monitors have been used for both processing and entertainment purposes.
Today’s monitors are moving away from liquid-crystal display (LCD) technology, which uses cold cathode fluorescent lamps (CCFLs) for backlighting. Developers are opting for light-emitting diode (LED) technology instead, which uses much smaller, brighter, and economically efficient light-emitting diodes to illuminate a screen.
Organisations such as Sharp are constantly innovating monitor technologies. It was the first business to successfully manufacture and mass produce ‘IGZO’ ultra-high-definition signage solutions. The monitors utilise artificial transparent crystalline oxide semiconductors, composed of idium, gallium, zinc, and oxygen for a more energy efficient and well-lit 4k display.
Laptops
A laptop is a portable computer, suitable for use while travelling and working on the move. They generally offer the same capabilities as desktop devices, but cost more due to their more compact and complex design.
When opened, the lower part of the device hosts the keyboard, whilst the upper part houses the screen. Laptops have integrated screens, speakers, keyboards, trackpads, processors, memory, integrated webcams and microphones, some laptops also use touchscreen technology.
They tend to run on AC power or batteries, such as NiMH, Nicad or Li-ion packs, allowing them to be used unplugged for several hours until needing to be charged again. Apple Mac laptops have a magnetised power port instead of the standard plug-in power cord.
Thin Clients
A thin client is a basic lightweight computer specifically created to connect into a server remotely, usually via desktop virtualisation and cloud environments. They contrast with conventional PCs in functionality; thin clients are heavily reliant on another computer (server) to be useful, whereas PCs can perform computational tasks alone.
Thin clients can be used to enter shared sets of virtual applications, and shared or virtual desktops, to process data or access vast amounts of stored data.
Tablets
A tablet computer, is a flat thin mobile computer with a touchscreen display. They are typically larger than, but strongly resemble, smartphones, using touch technology to navigate rather than a keyboard or a mouse.
The format of a tablet was conceptualised in the mid 20th century, however it wasn’t until April 2010 when Apple released the first mass-market tablet – the iPad. Since then, the popularity of tablets has grown rapidly, becoming one of the most popular devices for both personal and workplace applications.
There are seven distinct categories of tablet produced today, each defined by internal systems, size, and input/output compatibility:
Slate
Varying in size, slates start from 6 inches, with some exceeding 18 inches. The word slate implies a flat surface and an overall sleek and thin device. It is for this reason that slate tablets are designed to be held in one hand while the other interacts with the device.
Mini Tablet As the name suggests, mini tablets are a smaller and lighter version of their larger counterparts, typically between 7-8 inches.
Phablet
A phablet is a ‘crossover mobile phone’ with touch-screens larger than 5 inches. Crudely naming these devices as phablet (a blend of the words phone and tablet), companies develop these products for people that prefer a larger screen on their mobile phone devices.
Convertible
There are three types of convertible tablet. Generally, they are devices that blur the line between a tablet and laptop. A defining feature of a convertible tablet is a keyboard, with standard convertibles having a keyboard built into the framework, these tablets are called convertibles because the keyboard can be folded away when it is not needed, such as the Lenovo Yoga.
A hybrid has a keyboard that can be completely detached, even during use. Lastly a 2-in-1 can have a keyboard either detachable or built into the frame, these tablets are defined through their capability to run desktop operating systems.
Gaming Tablet
A gaming tablet is a modified touch-screen designed for gameplay. These tablets typically have a directional pad (D-Pad) attached to make the gameplay experience run more smoothly by giving greater user control.
Booklet
Usually in a clamshell design, booklet tablets have a touchscreen on the inside of both the upper and lower sections of the device. This technology can be folded like a laptop, making them capable of fitting into a pocket, also allowing users to open the device to reveal a large touchscreen surface area.
Customised Tablets
Customised tablets, usually for business customers, adapt the technology’s hardware or surface to accommodate a business’ needs.
E-readers
E-readers are essentially tablets designed specifically for reading digital e- books and other published works, such as periodicals. Also known as e-book readers, any device that displays text on a screen can be described as an e- reader. Tablets that have been specialised and optimised for reading e- materials are marketed around their portability, readability in different levels of light, and battery life, they are also capable of holding thousands of books but often weigh less than one.
Interactive Screens
Large interactive touchscreens, touch tables, and touch walls are essentially much larger versions of handheld tablets, and were made popular in 2008 when Microsoft unveiled its ‘Surface’ table top. They are usually made with a panel of glass, which is coated in a transparent conductor such as indium tin oxide, and more modern interactive screens allow multi-touch functionality, meaning the screen can detect more than one touch-point.
There are five common types of touchscreen technology used today: 5-wire resistive, surface capacitive, projected capacitive, surface acoustic wave, and infrared.
- 5-Wire Resistive – uses two metallic layers that register touch when pressed and come into contact• Surface Capacitive – uses a transparent electrode layer of glass which recognises touch using the static electricity generated by the human body
- Projected Capacitive – works in the same way as surface capacity, but also allows the user to wear surgical or thin cotton gloves
- Surface Acoustic Wave – creates an invisible grid of ultrasonic waves on the surface, which when broken by touch partially absorbs the wave and allows the receiving transductor to locate the touch-point
- Infrared – uses IR emitters and receivers to create invisible grids of light on a surface, which when interrupted by touch allow the internal computer to pin-point where it was broken.
Interactive screens are fast becoming the ultimate communication medium in areas such as: control rooms, education, broadcast studios, training rooms, video conferencing environments, boardrooms and as interactive public signage. They come in all shapes and sizes, with standard screens being 70 inches, up to 100 inches.
Mobiles
A mobile phone is a portable telephone that makes and receives calls over a radio frequency. These devices, which many people today say they ‘can’t live without’ have only existed for the last 44 years.
The first handheld mobile phone was introduced to the world in 1973 by Motorola, weighing 2kg. The first commercially available mobile phone did not appear until 1983 however – the Motorola DynaTac 8000x.
In the decade following DynaTac 8000X, mobile phone technology developed rapidly. Devices with advanced mobile operating systems now dominate the consumer market, combining the features of a personal computer with extra features useful for handheld use. Smart devices or ‘smartphones’ have access to the internet, and often come with features such as a media player, GPS navigation and a digital camera, all integrated into one compact device.
Servers
A server is a computer program or device that provides functionality for other programs or devices.
Servers are typically classified by their purpose, for example:
- A web server is a computer program that serves requested HTML pages or files for internet access.
- An application server is a framework that allows applications to be created and used, an application will run on the app server.• A proxy server acts as an intermediary between a device and another server from which a user or client is accessing information.
- A mail server is software that receives incoming e-mail from local users and remit senders, and forwards email for delivery.
- A virtual server is a program that runs on a shared server, configured in a way that the server does not appear shared.
Network Attached Storage
NAS drives allow users to access files from both inside and outside of the office or home, making them ideal for storing documents, music and video collections.
NAS drives allow you to store large amounts of data. The main reason people purchase NAS drives is for media playback. A NAS drive enables users to play media on TVs without having to connect to a computer. They use much less power than a regular PC too, which makes them cheaper to run.
Projectors
A projector is an output device, like a monitor, that takes images generated by a computer and reproduces them onto a surface that is usually large, flat and lightly coloured. Projectors can be used for presentations or films, as they are able to produce either stills (slides) or moving images (videos).
Projectors use either HDMI or VGA cables from a computer as their input.
The first projector was produced in 1965, this was a carousel slide projector. The digital projector we know today was first produced in 1984, but the technology is being constantly changed and innovated. A projector invented by Ricoh in 2012 allows users to project a screen up to 80 inches, from a distance of just 20cm from the projected surface.
Commercial Displays
Commercial displays are designed for businesses, rather than the home market. These screens are quickly replacing projector technology in audio/visual environments, particularly in classrooms and boardrooms.
Possibly one of the most exciting areas of growth in technology is in the area of Audio Visual (AV) and interactive products, which can quickly turn an ordinary business meeting or lesson into an impressive presentation or proposal.
These screens tend to work on a ‘plug and play’ method, allowing users to plug in their laptop, tablet or USB into the screen and display exactly what they want. They can also be integrated with conferencing software, allowing colleagues across the globe to tune into a meeting.
Wireless Access Points
In computer networking, a wireless access point (WAP) is a type of hardware that allows a Wi-Fi ready device to connect to a wired network by connecting the WAP to a router and sending out radio signals that wirelessly connect the device. Prior to wireless access to networks, setting up a network that everyone could connect to in a business required miles of cables running through walls and ceilings.
Types of Software
Short range wireless broadband technology, also known as Wi-Fi is the essential piece of technology required for people around the world to access the internet, wirelessly. From schools and offices to homes, coffee shops and even cars, Wi-Fi is at the heart of modern connectivity.
The pace of Wi-Fi integration into modern devices now means that the internet can be accessed on: personal computers, video games consoles, digital cameras, tablets, mobile phones, digital audio devices and modern printers.
The signal strength and range of a Wi-Fi transmitter, such as a router, is determined by the environment. The typical range is around 20 metres indoors, but can be much further outside, this is largely due to no objects, such as walls or metals blocking or weakening the signal. Some devices can share Wi-Fi transmission via an ad hoc Wi-Fi transmission, commonly known as a HotSpot, which is where a device creates a small Wi-Fi signal around itself. This is useful if the user is in an area with no Wi-Fi, they can use devices that have internet access via 3G or 4G, such as their mobile phone to create a Wi-Fi hotspot, enabling them to access the internet on a non-networked device such as a laptop.
Web Filter & Security
A web filter is a program that screens incoming web pages to determine whether the content should be displayed by the user. The filter checks the origin or content of the page, against a set of rules provided by a company or person who has installed the filter.
The type of content or pages that are targeted by web filters include: objectionable advertising, spyware, viruses and pornographic content.
Web filters reduce recreational internet surfing among employees and students, whilst securing networks from web threats. Web filters are also popular in schools because they protect pupils from adult content, prevent them from accessing social media or from being reached by people that may wish to harm them.
Hosted Desktops
Switching to a hosted desktop is another mainstay for organisations conscious of protecting their business’ data. A hosted desktop is a form of virtual space that uses the internet to store business data securely in the ‘Cloud’ – a computer-generated storage space. It gives instant and secure access to business software, documents, and files from anywhere in the world, at any time. A hosted desktop is particularly useful for organisations that wish to save money by removing the need to fund IT support and multiple sets of hardware, such as servers. It is also a useful tool for large corporates or mobile workers that need a lot of people to be able to access files remotely, enabling collaboration within the virtual environment. Perhaps the biggest motive for choosing a hosted desktop is security. Some providers will store business data in a UK data centre, meaning it cannot be accessed by hackers because of strict data protection laws. Therefore, selecting the right provider is vital.
Office 365
Office 365 is the umbrella brand name given toMicrosoft’s package of software and service subscriptions, that can be used on both Windows and Mac operating systems. Office 365 provides cloud storage space on its OneDrive platform and 60 minutes of Skype minutes each month.One of the main functions of Office 365 is email. Connecting employees and customers via the internet, the 365 package also provides access to the below software applications:One of the main functions of Office 365 is email. Connecting employees and customers via the internet, the 365 package also provides access to the below software applications:
- Word – A word processor
- Excel – A type of software for creating data spreadsheets
- Powerpoint – A programme for creating presentations• Microsoft Access – A database management system• Outlook – A personal information manager, including: email, a calendar function, task manager, and an address book
- OneNote – A note taking programme that collects handwritten or typed notes, drawings, audio commentaries, and screen clippings• Publisher – A desktop publishing application for designing work
- Skype for Business – A communications client used for conferences and meetings in real-time
- Project – A project management application
- Visio – A diagram and flowcharting application
Computer Security Threats
Malware
Short for malicious software, malware is the umbrella term used to describe a variety of intrusive or hostile software including: worms, viruses, trojan horses, ransomware, adware, scareware, and spyware. It is widely believed that the first malware software was written as a prank or experiment. Today however, malware is used for more sinister means by hackers or governments to steal financial, personal, or business information.
Virus
A virus is a type of malevolent programme that replicates itself by altering other computer programmes and implanting its own code. With the main motives for creating acomputer virusincluding: to send a political message, for personal amusement, to demonstrate software vulnerabilities, to seek profit, or for sabotage, viruses cost businesses billions in economic damage annually.
Spyware
Spyware can be categorised into four different types – system monitors, trojans, adware, and tracking cookies. Essentially spyware is software that intends to gather personal or business information without the victim’s consent or knowledge, or to gain control of a device in secret.
Ransomware
Ransomwareis software that aims to block the victim from accessing their files, or threatens to publish sensitive information unless a ransom is paid. Even simple forms of the software are so sophisticated that a knowledgeable person would struggle to reverse it.
Phishing
By disguising itself as trustworthy,phishingis the name given to attempts at gaining information such as passwords, credit card details, and usernames for malicious purposes. Phishing is usually carried out in the form of an email or instant message that directs the victim to a fake website that looks identical in appearance and feel to the original.
Social Engineering
Social engineering is the term used to describe an entity obtaining the confidence of the victim for the purpose of gathering information, committing fraud, or gaining access to a system. Within an IT setting, social engineering means the psychological coercion of a person into divulging confidential information or performing actions. It differs from what people consider to be a traditional ‘con’ because many steps are involved to get the desired outcome.
Spam
Spam, or spamming, is the use of electronic messaging systems to send unsolicited advertising or messages repeatedly to a person or on a website. The name spam originates from a Monty Python sketch, in which the luncheon meat spam featured in every recipe, and most people use the term spam to refer to excessive or unwanted emails.
https://www.youtube.com/watch?v=anwy2MPT5RE– Spam by Monty Python
Password Cracking
Quite simply,passwordcracking is the recovery of passwords or data through repetition for the purpose of gaining unauthorised access to a system or to recover a forgotten password.
Browser Hijackers
A browser hijacker is a form of malicious software that aims to modify a user’s web browser settings by injecting advertisements onto their homepage without consent. The software may replace the victim’s error pages, home page, or search pages with its own, which are often used to drive traffic to a particular website. Some browser
hijackers will be slightly more dangerous and install keylogger software that tracks entered bank details, authentication details, and passwords.
Computer Worm
A computer worm is a type of malware with the singular purpose of replicating itself in order to spread to other computers and devices. It often exploits weaknesses in the target device’s security in order to gain entry.
Anti-Virus
Also known as anti-malware software,anti-virus softwareis a type of computer software that is installed to prevent, detect and remove malicious software.
Antivirus was originally developed to detect and eradicate computer viruses, however modern antivirus software can protect computers from other threats including: browser hijackers, ransomware, worms, fraud tools, infected and malicious URLs, spam, phishing attacks and many more.
Antivirus software use many different methods to protect computers, they often search for signs of viruses in websites that are visited, as well as conducting regular scans of all data and files on a computer’s hard drive.
Some people believe that having multiple anti-virus software will add more protection, however, the two different antivirus software can interfere with each other and provide lower protection.
Anti-Virus Providers
With the rise in use and sophistication of malicious software, there has also been a drastic increase in the number of companies that focus their core offering around computer system defence.
AVG
AVG Technologies is a software development company that focusses on system security. Founded by Jan Gritzbach and Tomas Hofer in 1991, AVG is now headquartered in Amsterdam, The Netherlands. The company has over 200 million active users of its products, which include performance optimisation software, personal privacy and identity protection applications, and internet security software.
As of 2016, AVG Technologies became a subsidiary of fellow software developers Avast Software.
McAfee
Named after its founder John McAfee in 1987, McAfee was established to provide digital security tools for personal computer users and server devices. McAfee Inc., as it is known today, is an American computer software company that offers its service worldwide, and is one of the world’s largest security technology companies in both revenue and market share.
Norton
Anti-virus developer Norton was acquired by the Symantec Corporation in 1990. During Symantec’s 2014 restructuring, which split into two businesses with separate core functions, Norton was incorporated into the area that focussed on security, whilst the other offers information management systems.
Kaspersky
Kaspersky Laboratories is a Russian cyber security and anti-virus company headquartered in Moscow. The multinational corporation was founded by the current CEO Eugene Kaspersky, and operates from a holding company in the UK. Kaspersky’s core offering is the development of anti-virus software,endpoint security, password management, and internet security systems, giving it the largest market-share of cybersecurity software in Europe as of 2016, with 400 million users.
Lavasoft
Founded by Nicholas Stark and Ann-Christine A Kerlund in 1991, Lavasoft is a software development corporation that provides malware and spyware detection software, such as their flagship product Ad-Aware. Ad-Aware is able to detect spyware, viruses, dialers, Trojans, bots, and hijackers.